When evaluating alarm systems—whether you’re building security solutions for your customers or assessing options for your home or business—you’ll likely come across providers offering alarm monitoring services. At first glance, this may sound like just a fancy way to describe alarm systems, but it’s so much more.
Alarm monitoring services add a professional response layer to security systems, connecting alarms to real-time verification and emergency services when a threat is detected.
There are a few different types of alarm monitoring that follow these workflows, including professional monitoring, self monitoring, and on-demand monitoring like Noonlight. Here’s what else you need to know.
What Is an Alarm Monitoring Service?
Alarm monitoring services provide professional security surveillance that alerts police, fire, or other emergency services when an alarm or sensor is activated. Also called central station monitoring or remote monitoring, these services are connected via internet, phone, or cellular lines to a monitoring center staffed with agents that review, verify, and act on detected threats.
The difference between an alarm system and alarm monitoring is that the alarm system is the hardware (think: cameras, sensors, lights), while alarm monitoring is the service layer that connects those systems to real-time response.
Alarm monitoring is used in both homes and businesses, though systems vary in complexity. Monitoring for homes typically focuses on intrusion and fire alerts, while businesses often include more advanced capabilities like video monitoring and access control.
Types of Alarm Monitoring Services
There are a few different variations of alarm monitoring services, each representing a different operational model for how alarms are handled, verified, and escalated; ranging from 24/7 professional monitoring to on-demand solutions like Noonlight.
1. 24/7 Professional Monitoring
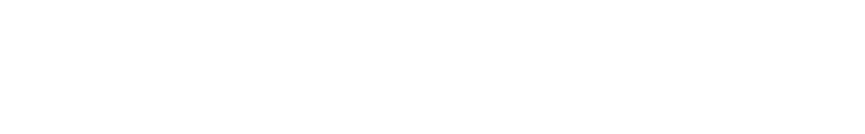
Professional video monitoring is likely what you think of when you envision a monitoring center: a staffed center, with professional agents reviewing alarms and escalating to emergency services when needed. This level of monitoring is integrated into existing alarm hardware, and may be part of a monthly subscription.
While this has traditionally meant continuous, human-led monitoring, modern professional monitoring can also be delivered through event-driven models—where trained agents respond to verified incidents as they occur, rather than actively watching live feeds at all times. This often leads to a faster, more accurate, and more cost-efficient outcome.
This model provides continuous oversight and a dedicated response layer for handling alarms, making it a common choice for systems where constant monitoring is required.
2. Self-Monitoring
Self-monitoring is exactly what it sounds like—a surveillance system that bypasses the central station and leaves monitoring and escalation up to the user. Here, alerts go directly to the user (typically via an app on their mobile device), where they can decide what warrants escalation or contacting emergency services.
While this approach offers more direct control, it also places the responsibility of filtering and responding to alerts on the user. Many systems send alerts for everything, from wandering animals to wind-blown debris; which can make it difficult to quickly filter through, identify, and act on real threats.
3. On-Demand or App-Based Monitoring
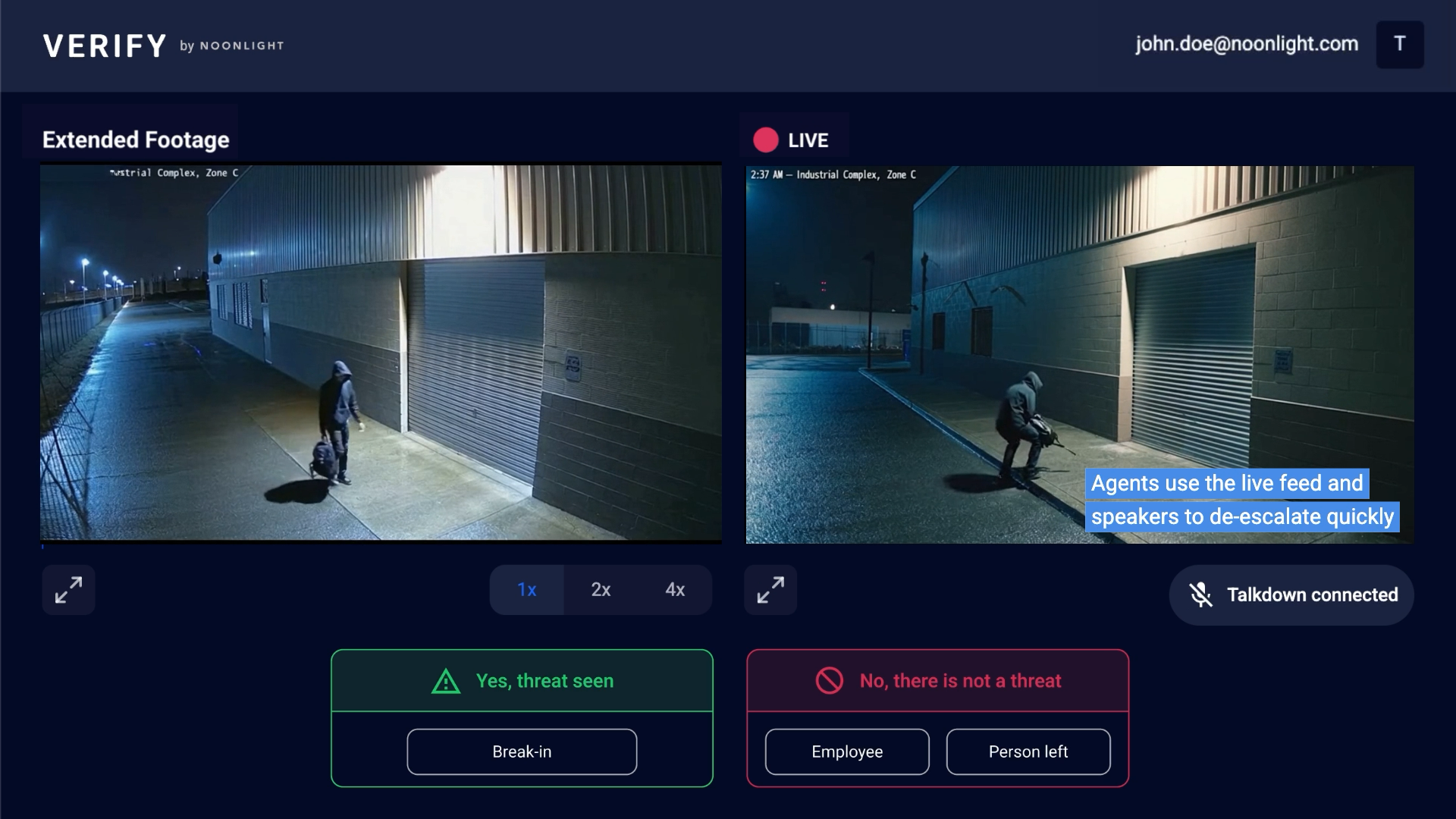
The third type of alarm monitoring is perhaps the most flexible. App-based or on-demand monitoring, like the solutions offered to security providers by Noonlight’s Verify API, is a mobile-first safety approach that is only active when needed.
Verify, and other solutions similar to it, operate by detecting and verifying threats before they’re escalated. Noonlight-verified agents review video footage and make the judgement call whether the footage represents an actual threat (like a break-in at a construction site) or not (like a stray animal wandering through a parking lot). If contacting emergency services is warranted, the end user is contacted and has control over cancelling a 911 call.
This model combines professional verification with greater flexibility, reducing the burden of constant monitoring while still ensuring that real threats are identified and acted on.
What Do Alarm Monitoring Services Include?
Exact detection services will differ depending on the alarm monitoring service provider and the needs of the end user. Generally, alarm monitoring services can support capabilities like:
- Intrusion detection
- Mobile monitoring and alerts
- Fire or smoke alarm monitoring
- Carbon monoxide alerts
- Medical device integration
How Alarm Monitoring Works
While the exact process differs from provider to provider, here’s a general overview of how alarm monitoring works for monitored systems.
1. Alarm Is Triggered
To activate alarm monitoring, an alarm needs to be triggered, whether a motion-activated sensor, a panic button, or an alarm on an open door or window. Once activated, the sensor sends a signal to the monitoring center.
2. Signal Is Sent to Monitoring Center
This signal is sent to the monitoring center—or in cases of self-monitoring, the user’s mobile device—via cellular, Wi-Fi, fiber optics, or landline.
3. Monitoring Center Verifies the Alert
For professional and on-demand monitoring, the alarm is reviewed by central station agents and escalated to emergency dispatch if needed.
In systems that incorporate verification layers, like Noonlight, users can be contacted via app, text, or call and are given the opportunity to cancel alarms before they are escalated.
4. Emergency Response Is Dispatched
Once the alarm has been verified, monitoring agents alert and dispatch police, fire, or medical services as necessary.
For systems integrated with Noonlight, this entire process takes a median of just 141 seconds—about two minutes, based on Noonlight platform data—highlighting how verification and streamlined workflows can lead to faster, more effective response when it matters most.
Why Modern Alarm Monitoring Matters
Much like the security industry at large, alarm monitoring has gone through several key changes in recent years—but the need for it has only grown. This process has evolved beyond simply triggering an alarm, enabling faster, more accurate, and more flexible responses when it matters most.
Faster, Verified Response
Verification methods have evolved significantly. Instead of always having to call a user to verify an alarm or address, modern alarm monitoring providers can now reach users via app, push notification, text, or call, helping ensure they’re contacted faster and alarms are resolved more efficiently.
Actionable Alerts, Not Just Noise
Traditional alarm systems can create uncertainty over whether an alert is real or a false alarm. Modern monitoring helps turn those signals into actionable events, with clearer verification and escalation steps, so the right response can happen without unnecessary delay.
Flexible, On-Demand Protection
Instead of relying only on always-on systems, more providers now offer customizable, flexible approaches where alarm monitoring is active only during certain hours or when it’s needed. This can reduce costs, lower operational burden, and improve overall effectiveness of the system.
Coverage Beyond Fixed Hardware
Security systems that are rigidly fixed in one place are no longer the only option. Mobile-first approaches make it possible to extend protection beyond a single location, helping users stay connected to monitoring services wherever they are.
Built for Integration
Alarm monitoring is no longer tied to a traditional security system. Services today are increasingly device-agnostic and can be integrated into a wide range of platforms, personal safety products, and mobile devices—making them more adaptable to different use cases.
Is Alarm Monitoring Right for You?
Alarm monitoring shouldn’t be viewed as a standalone feature; rather, it’s a critical layer in a complete security system. As systems have evolved, monitoring has become more flexible, more accurate, and more adaptable to different environments and use cases.
Solutions like Noonlight build on this approach, offering a modern, verification-driven model that can integrate into a wide range of devices and systems while enabling faster, more reliable emergency response when it matters most. Learn more about Noonlight’s strategy for flexible, modern alarm monitoring.
Frequently Asked Questions
Do I need alarm monitoring if I already have an alarm system?
Yes. An alarm system and alarm monitoring serve different purposes. An alarm system detects events—like motion, a door opening, or smoke—but it doesn’t automatically ensure a response.
Alarm monitoring adds a response layer, connecting those alerts to a monitoring center or verification system that can assess the situation and contact emergency services if needed. Without monitoring, alerts may go unnoticed or require manual action.
Can I monitor my alarm system myself?
Yes, many systems offer self-monitoring, where alerts are sent directly to the user’s phone or device. This provides full control over how to respond, but it also means you as the user are responsible for reviewing alerts and deciding when to escalate.
In practice, this can be challenging—especially if alerts are frequent or occur when you’re unavailable to step in. That’s why some systems combine self-monitoring with verification or professional support to help filter and prioritize real threats.
What’s the difference between traditional and app-based alarm monitoring?
Traditional alarm monitoring typically relies on fixed hardware systems connected to a central station that verifies alerts, often through phone calls. App-based monitoring builds on this model by adding mobile-first communication and more flexible activation.
Users can be reached through app notifications, text, or calls, and monitoring can be enabled on-demand rather than always running. This can improve response speed, reduce false alarms, and provide more control over when monitoring is active.
How do modern alarm monitoring services integrate with existing systems?
Modern alarm monitoring services are often designed to be device-agnostic and integration-friendly. Instead of being tied to a single hardware system, they can connect to a wide range of sensors, cameras, and platforms through APIs or cloud-based infrastructure. This allows monitoring capabilities to be embedded into existing products, apps, or security systems without requiring a complete overhaul.
Can alarm monitoring be embedded into apps or platforms?
Yes. Many modern alarm monitoring solutions are designed to be embedded into apps, devices, or platforms. Through APIs and cloud-based services, monitoring can be integrated directly into user workflows—allowing alarms to be verified and escalated within the context of an existing product. This approach makes it easier to extend safety features without building a monitoring infrastructure from scratch.
How does verification improve alarm monitoring accuracy?
Verification helps determine whether an alarm represents a real threat before emergency services are contacted. This can involve reviewing sensor data, video footage, or contacting the user through multiple channels.
By filtering out false alarms—like environmental triggers or non-threatening activity—verification improves accuracy, reduces unnecessary dispatches, and helps ensure faster response for real emergencies.